Christina Lekati, social engineering training
Christina Lekati is a psychologist and a social engineer. She specializes in the mechanisms of behavior, motivation, decision making, manipulation and deceit. She is an expert in human dynamics and passionate about social engineering.
Christina has also a master’s degree in International Business. True to her passion, her thesis on social engineering strategies earned her a distinction during her graduation.
Contrary to typical career paths, her history and involvement in the security field started quite early in her life. Being raised by George Lekatis, a sought-after risk management and cyber security expert, she found herself magnetized by the security field at a very young age. Growing up, she was able to get involved in different projects that gave her an edge in her own knowledge and experience.
Christina has participated among other things in penetration tests, in trainings to companies and organizations, in vulnerability assessments, in profiling and analysis of the modus operandi, and in the process of identifying personality traits, behavioral tendencies, and demographic variables of offenders based on characteristics of illegal acts. She is working with Cyber Risk GmbH as a social engineering expert and trainer.
Christina is the main developer of the social engineering training programs provided by Cyber Risk GmbH. Those programs are intertwining the lessons learned from real life cases and previous experiences with the fields of cybersecurity, psychology, and counterintelligence. They often cover unique aspects while their main goal is to inspire delegates with a sense of responsibility and a better relationship with security.
Being committed to sharing knowledge and expertise, Christina is also a speaker. She participates in a variety of cyber security events, raising awareness and educating people on social engineering techniques and the psychological elements involved in human hacking.
She is also an active Advisory Board Member at the OSINT Curious project, contributing to the international scene of Open Source Intelligence (OSINT) with the latest news, updates and techniques on collection and analysis.
For updates, news, and insights, you can follow her on Twitter (@ChristinaLekati).
You may find some of Christina’s contributions to the international cybersecurity scene below:
1. Christina Lekati, interview, Schweizer Radio und Fernsehen (SRF): “Social Engineers und ihr Lieblingsnetzwerk”.
Beim Social Engineering geht es darum, Menschen zu manipulieren, um an Infos oder Geld zu kommen. Kaum ein Hackerangriff kommt heute ohne eine gute Portion «Human Hacking» aus. Wie funktioniert es, was kann man dagegen tun und welche Rolle spielt LinkedIn?
https://www.srf.ch/audio/digital-podcast/social-engineers-und-ihr-lieblingsnetzwerk?id=12484536
2. Christina Lekati, October 2023, presentation at the Swiss Cyber Storm (Bern, Switzerland): “Targeting Key Individuals, Profiling, and Weaponizing Psychology.”
Targeted social engineering attacks that weaponize psychology have become tools employed by State-sponsored adversaries and cybercriminals. They want to infiltrate organizations, steal information, recruit insiders, and move to other critical infrastructure entities. What must individuals with privileged access to information or systems do?
https://www.youtube.com/watch?v=_qbJvjsRAPo

3. Christina Lekati, November 2023, 2 days training at the DeepSec Conference in Vienna, Austria: “Security Intelligence: Practical Social Engineering and Open-source Intelligence for Security Teams”
In this rapidly evolving threat landscape, security professionals and penetration testers / red teamers must understand better how social engineering works, and how to identify and disrupt attack verticals.
https://deepsec.net/schedule.html
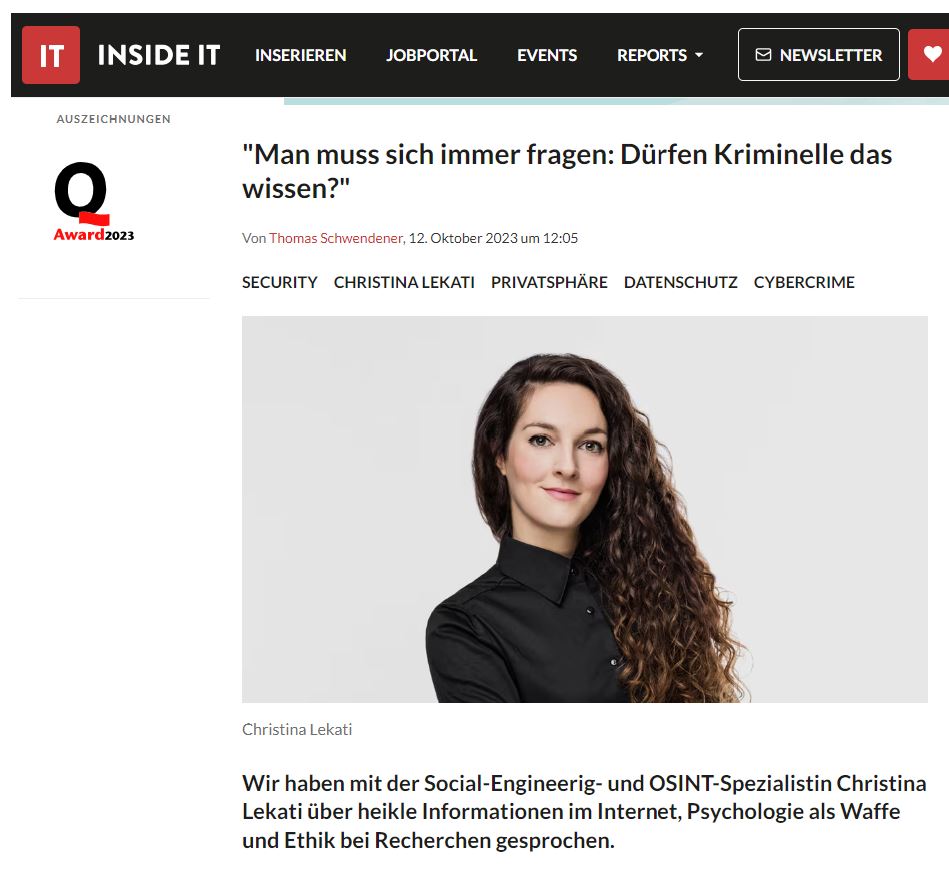
4. Christina Lekati, October 2023, interview for the Swiss “Inside IT” News Platform: "Man muss sich immer fragen: Dürfen Kriminelle das wissen?"
Am Ende hängt doch alles am Menschen: Wenn man sein Passwort weitergibt, die Zweifaktor-Authentifizierung ausschaltet oder Geld an Kriminelle überweist, nützt ein ausgeklügeltes Sicherheitssystem wenig. Und auch wenn es abgedroschen klingt: Der Faktor "Mensch" wird oft noch unterschätzt, besonders wenn man sich vergegenwärtigt, wie viele heikle Informationen im Netz publiziert sind. Und wie einfach diese mittlerweile mit den richtigen Tools und Methoden gesammelt werden können – raffiniertere Google-Befehle genügen bereits für erstaunliche Resultate. Wenn die Angreifer dann noch über grosse Ressourcen verfügen, wird es richtig düster. Wie das geht, weiss Christina Lekati, Spezialistin für Social Engineering und Open Source Intelligence (OSINT). An der diesjährigen Swiss Cyber Storm in Bern wird sie über den "Human Factor" sprechen. Wir haben uns im Vorfeld mit ihr unterhalten.
https://www.inside-it.ch/man-muss-sich-immer-fragen-duerfen-kriminelle-das-wissen-20231012
5. Black Hat Asia 2023. Christina Lekati and Samuel Lolagar lead the class: “Fundamentals of Cyber Investigations and Human Intelligence” at Marina Bay Sands, Singapore.
In this class, participants learn a comprehensive methodology for gathering in-depth information on a human target, following three intelligence disciplines:
• Open-source intelligence (OSINT),
• Social media intelligence (SOCMINT), a sub-brunch of OSINT,
• Human intelligence (HUMINT), and particularly, virtual HUMINT.

6. Presentation at the Insomni’hack conference in Lausanne, Switzerland, in 2023: “Targeted Social Engineering Attacks: Weaponizing Psychology”.
Targeted social engineering attacks that weaponize psychology have become tools employed by cybercriminals to infiltrate organizations in the public and private sector, steal sensitive information, recruit insiders, and help threat actors breach an organization's security. This presentation covers some of the most recent social engineering techniques and case studies.
https://www.youtube.com/watch?v=SfBj0xnd_XI

7. Featured for her presentation at the Insomni’hack conference in LeTemps, one prominent newspaper in Switzerland, March 2023.
“The Insomni'hack conference, organized at EPFL, highlights ultra-sophisticated phishing techniques. Explanations from cybersecurity specialist Christina Lekati”
https://www.letemps.ch/economie/hackers-usent-psychologie-fine-pieger-leurs-victimes
8. Article for Golem.de (in German): “ChatGPT und die Zukunft des Social Engineering”.

9. Article for Heise’s iX Magazine (in German): “Sicherheitsrisiko Mitarbeiter: Mit Psychologie Cybersecurity-Kultur Schärfen Der Mensch ist das schwächste Glied in der IT-Security-Kette. Psychologisches Know-how hilft beim Aufbau einer Cybersecurity-Kultur.”

10. Expert opinion for an article of Die Zeit (in German): “Hier Spricht die Polizei". Telefonbetrüger geben sich als Beamte von Europol aus, um Geld zu erbeuten. Unsere Autorin hat mit einigen gesprochen – und mit einem Opfer, das mehr als 30.000 Euro verloren hat.
https://www.zeit.de/2022/25/telefon-betrug-europol-polizei
11. Podcast Interview for Hensoldt Analytics: “Social Engineering and the Protection of High-Value Targets.” In this podcast episode we discuss the risks posed by social engineering, and how OSINT can be used for the protection of high-value targets.
https://www.youtube.com/watch?v=d2do-JGzw8c&list=PLfodXJHGJlWm06UItlJ-hNAhvF1CZxy9r&index=7
12. Article for Feedly’s Threat Intelligence Community “Ahead”: “Social Engineering Kill-Chain: Predicting, Minimizing, & Disrupting Attack Verticals.” Protecting an organization from social engineering attacks is NOT an easy, or one-dimensional task. This is an asymmetric game in which information, knowledge, & strategy are paramount. But how do threat actors build their attack strategy, and how can we inform ours? This article explains and breaks down the typical social engineering kill-chain, and offers practical tips for a defense strategy.
13. Article for Feedly’s Threat Intelligence Community “Ahead”: “High Value Targets (HVT): Where Should You Focus Your Intelligence Collection & Analysis Efforts?” Ensuring the security of an HVT requires more than having adequate technical infrastructure or a close protection operative. That individual's public and private actions can directly impact their personal and organizational security. A protective intelligence report identifies weaknesses and informs the organization's security strategy. You may read the article for more details:
https://ahead.feedly.com/posts/high-value-targets-focus-intelligence-collection
14. SANS Summit Talk for the Open-Source Intelligence Summit (Washington DC): “Protecting High-Value Individuals: An OSINT Workflow.”
This presentation walks you through the workflow of a (sanitized) OSINT assessment case for a high value-target. This case revolves around a company executive a few days before moving into public announcements that were likely to trigger hacktivist groups.
Cyber harassment can start from online platforms but it may also continue into the physical sphere of the targeted individual. Most often, the goal is either to influence the behavior of the target and make them resign, change their decisions and future behavior, or to cause significant psychological distress – that will ultimately affect their work performance. Knowing that harassment was a highly likely scenario, the company requested an OSINT assessment on this individual to help them eliminate or manage information that could pose a risk to the individual and ultimately affect his performance and the company.
https://www.youtube.com/watch?v=rE4mORq9T5s
15. Interview for the State of OSINT. A community project that captures the views and experiences of some of the most renowned open-source intelligence practitioners. Read expert's views on the best (and worst) of OSINT, their favourite tools and techniques, and how they think the landscape is changing.
https://stateofosint.com/posts/2022-christina-lekati/

16. Presentation at the CEO corner and the CISO/DPO Cyber Day in Luxemburg, organized by PwC Luxembourg.
At the CEO Corner, Christina was invited for an executive briefing on the highly personalized, social engineering threats targeting CEOs and the Board of Directors, in an interactive, in-person session among a small group of select executives and CEOs.
During the CISO/DPO Cyber Day, Christina presented the evolving nature of social engineering attacks, what we should expect in the future, and how weaponizing psychology is currently a threat to information security. She recommended Target Vulnerability Assessments that will assist high value targets avoid or better identify and respond to weaponized psychology attacks against them or their organization.
17. Keynote Presentation for SecIT by Heise. In this presentation, Christina Lekati discussed the psychological elements and behavioural science involved in facilitating users to adopt better cybersecurity habits. She talked about the drivers of motivation, people’s perception of risk and reward, the psychology of wilful compliance, but also about common mistakes in the process. This presentation aided security managers and executives to more effectively communicate and implement the necessary cybersecurity policies and procedures that employees need to practice within their organization.
18. DEF CON 29, presentation at the Social Engineering Village. "Judging By the Cover; Profiling and Targeting Through Social Media".
The presentation demonstrated how attackers gather information through social media and utilize them to manipulate and victimize their targets, ultimately leading to a security breach.
19. Interview for the TAZ Newspaper (In German): Jeder hat eine Schwachstelle. Betrüger bauen Vertrauen auf, um an Daten oder Geld zu kommen. Welche Tricks sie dafür nutzen, erklärt Sicherheitstrainerin Christina Lekati.
https://taz.de/Sicherheitsexpertin-ueber-Social-Engineering/!5711020/

20. SANS Summit Talk for the Open Source Intelligence Summit (Washington DC): “Judging By The Cover - Profiling Through Social Media”. The talk demonstrates how attackers gather information on their targets through social media and utilize them to manipulate and victimize them – ultimately leading to a security breach. If you have a SANS account you may find the slides of the presentation by visiting:
https://www.sans.org/cyber-security-summit/archives

21. Interview for Golem.de (In German): Social Engineering: Die unterschätzte Gefahr. Die größten Schwachstellen in technischen Systemen sind bis heute Menschen. Social Engineers machen sich ihre Sorglosigkeit zunutze - und finden auf sozialen Netzwerken alles, was sie für einen erfolgreichen Angriff brauchen.
https://www.golem.de/news/social-engineering-die-unterschaetzte-gefahr-1908-142812.html

22. Interview for the Dot Magazine: “Creating a “Human Firewall” for IT Security”. Psychologist and social engineer Christina Lekati from Cyber Risk GmbH explains the psychological basis of phishing and how to arm staff with effective defenses.
https://www.dotmagazine.online/issues/securing-the-future/human-firewall-for-it-security

23. Interview for the ECO Association - Europe’s Largest Internet Association (In German): Social Engineering: Mitarbeiter stärker für IT-Security sensibilisieren. Mitarbeiter müssen lernen, wie sie auf diese Anfragen in einer angemessenen Weise reagieren können. Dies geschieht durch intensive Schulung. Sie müssen verstehen, dass das Thema: Sicherheit geteilte Verantwortung bedeutet und, dass sie eben einen Teil dieser Verantwortung mittragen.
https://www.eco.de/news/social-engineering-unwissenheit-am-meisten-ausgenutzt/

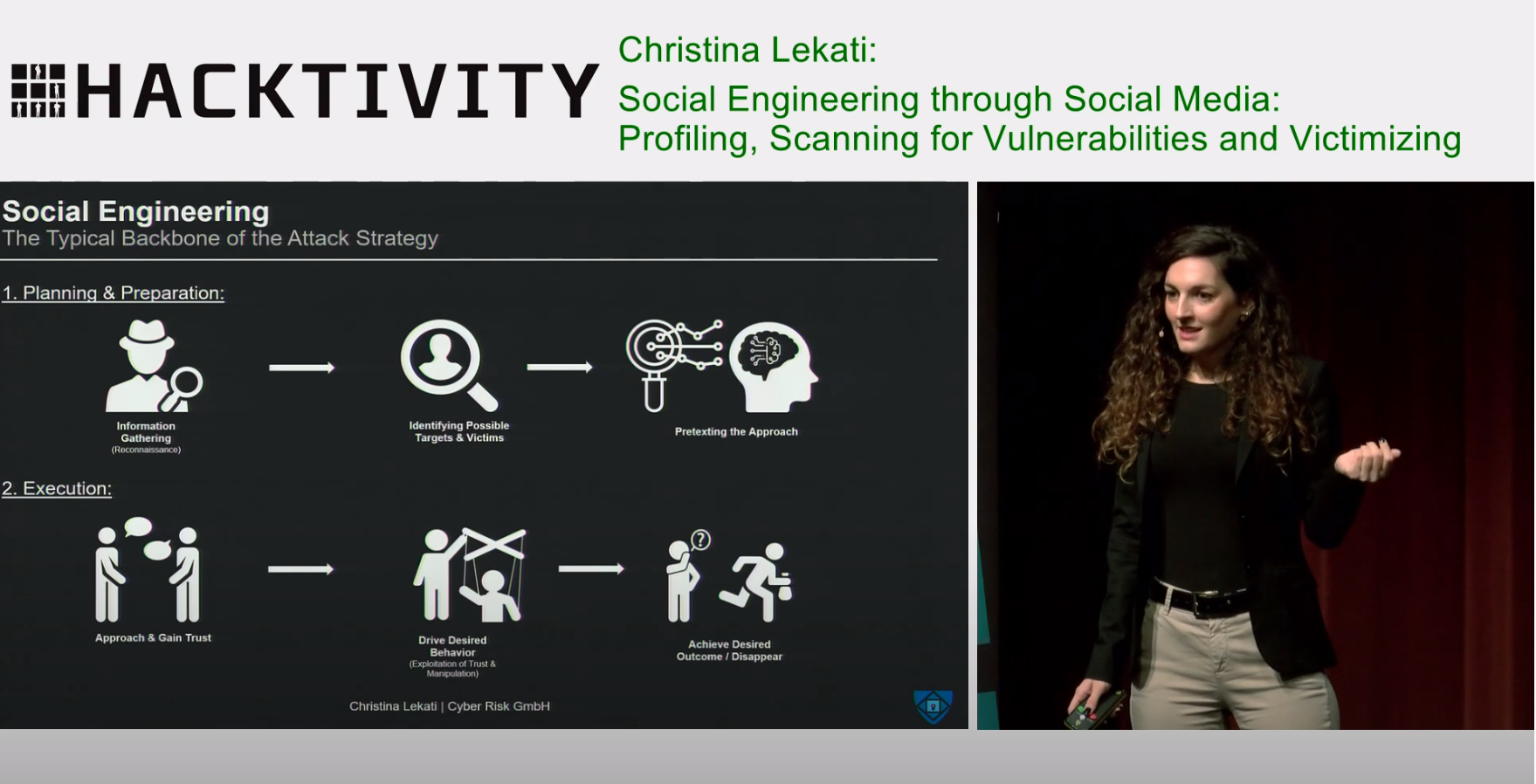
24. Conference Presentation at Hacktivity: "Social Engineering Through Social Media". The talk demonstrates how attackers gather information on their targets through social media and utilize them to manipulate and victimize them – ultimately leading to a security breach.
https://www.youtube.com/watch?v=D8Z69AsSFn0&t=577s
25. Conference Presentation at ElBsides Hamburg: "When Your Biggest Threat is on Your Payroll – Drivers and Enablers of Insider Threat Activities". The talk discusses the organizational factors enabling insider threat operations and countermeasures against them, by combining the lessons learned on insider activity prevention from the fields of counterintelligence, psychology, and cyber-security.
https://www.youtube.com/watch?v=5ovY0YlLZNU&t=2208s

26. Cyber Terror Campaigns Against High Value Individuals and Public Figures.
27. How Psychology and Behavioural Science Can Help You Build Your Cybersecurity Culture.
28. Wie Psychologie und Verhaltenswissenschaft ihnen beim Aufbau ihrer Cybersecurity-Kultur helfen können.
29. Psychological Exploitation of Social Engineering Attacks.
https://www.cyber-risk-gmbh.com/Psychological_Exploitation_of_Social_Engineering_Attacks.html
30. Psychologische Ausnutzung von Social-Engineering-Angriffen.
https://www.cyber-risk-gmbh.com/Psychologische_Ausnutzung_von_Social_Engineering_Angriffen.html
Our Services
Cyber security is ofter boring for employees. We can make it exciting.